- Advanced Infrastructure Penetration Testing
- Chiheb Chebbi
- 459字
- 2021-06-24 19:12:52
Open source intelligence
Open source intelligence (OSINT), as its name suggests, involves finding information about a defined target using available sources online. It can be done using many techniques:
- Conducting search queries in many search engines
- Gaining information from social media networks
- Searching in deep web directories and the hidden wiki
- Using forum and discussion boards
For example, if you want to search for a specific employee, you can use a theHarvester tool, and it will help find all public information about that person.
You can get theHarvester from its GitHub repository using this command from your console:
git clone https://github.com/laramies/theHarvester
Then, type ./theHarvester to run the script.
For example, if you want to collect information about a targetwebsite using Google search, simply run the following command:
theharvester -d targetwebsite.org -l 100 -b google
Here, the -l option is the limited number of results and -b indicates the search engine. In our case, we used the Google search engine:

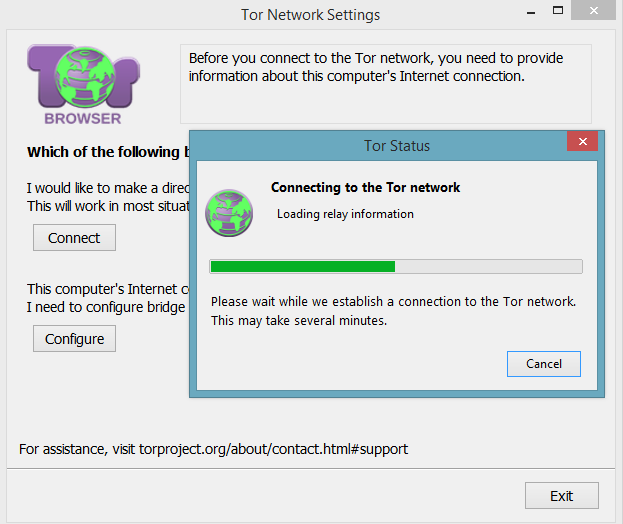
It is an advantage to gather information from the hidden web, not only for reconnaissance purposes but for competitive intelligence. To access the deep web, you simply have to download the Tor Browser via its official website https://www.torproject.org/ and install it. Open the browser and hit Connect to access the network:
Now, you are surfing the hidden web. You can use the hidden wiki for Tor websites from this link, http://wiki5kauuihowqi5.onion (they are represented as DomainName.onion), or simply use the DuckDuckGo search engine:

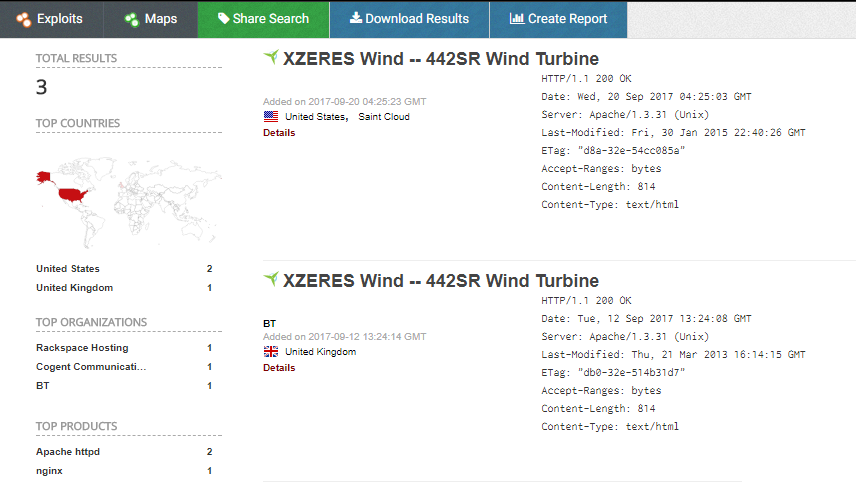
Not only you can search for personal identifiable information, but you can also search for online devices and even industrial control systems. For example, you can check www.shodan.io. This search engine will help you find devices online. The following screenshot is publicly available information about wind turbines searched by Shodan.io:
To discover the great potential of the Shodan search engine, let's take a glimpse into the power of this giant. First, go to www.shodan.io and create a new account:
Use the search bar to enter a search query, or you can simply hit a predefined category: Netcams, default password, dreambox, industrial control systems, and so on. This is a snippet of the most popular search tags:
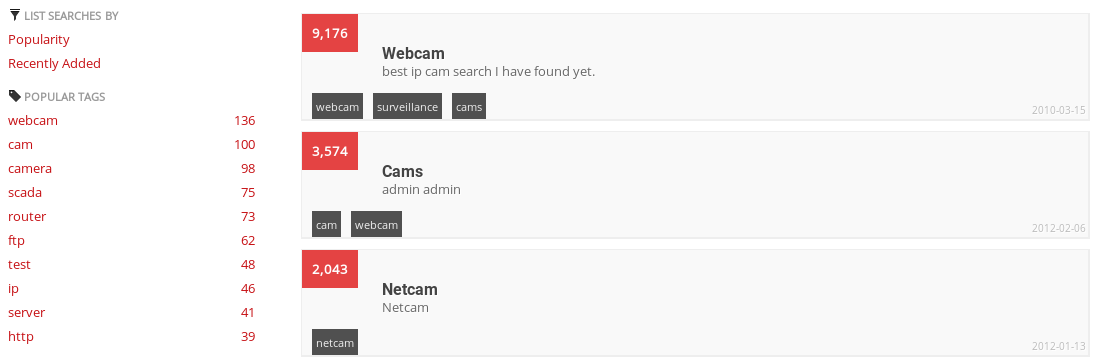
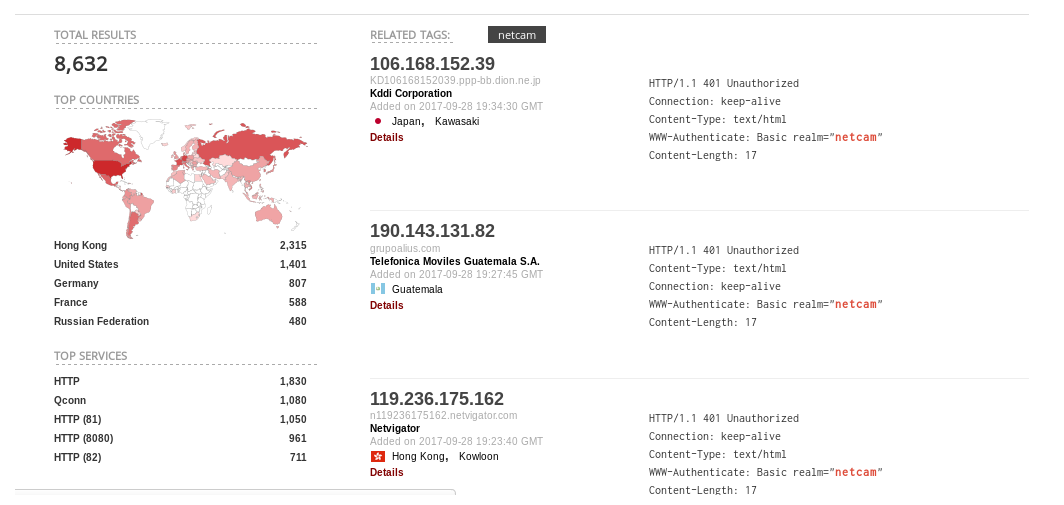
Let's hit Netcams as a demonstration. According to the screenshot listed as follows, the search engine found at least 8,632 publicly available sources of Netcam information, including their IP addresses with detailed descriptions about them:
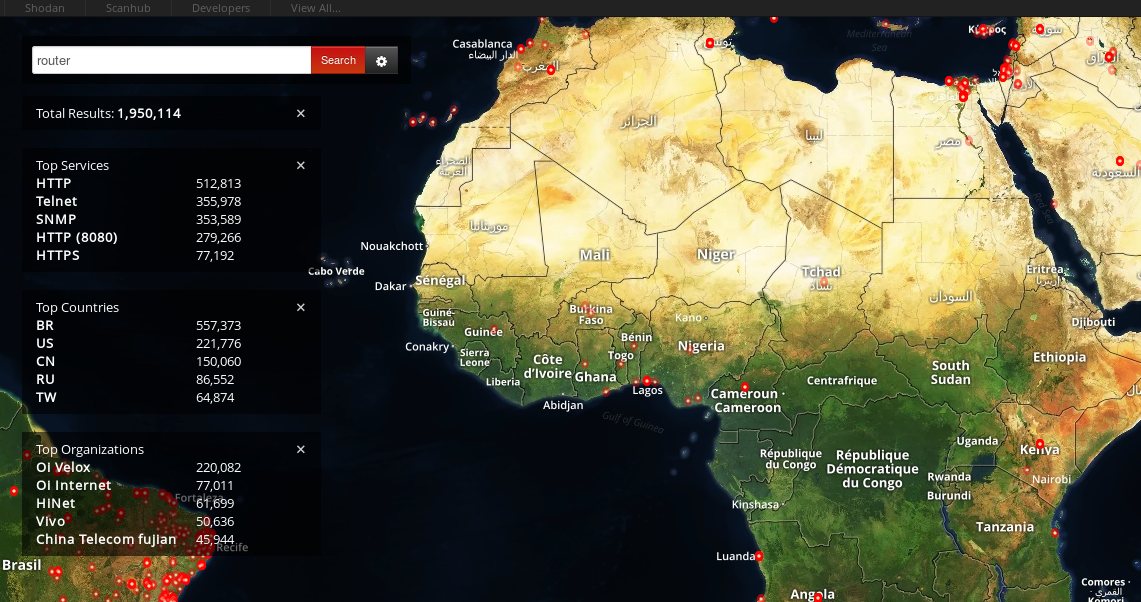
Also, you can use a real-time map to search online devices such as routers:
- PLC控制系統應用與維護
- 嵌入式應用程序設計綜合教程(微課版)
- SharePoint 2013 應用開發實戰
- 異質結原理與器件
- Python基礎教程(第3版)
- 從實踐中學習Kali Linux無線網絡滲透測試
- Advanced TypeScript Programming Projects
- iOS 8開發指南
- Python UNIX和Linux系統管理指南
- Distributed Computing with Go
- 從實踐中學習Windows滲透測試
- Mastering Windows 8 C++ App Development
- 嵌入式微系統
- Learn Quantum Computing with Python and IBM Quantum Experience
- OpenHarmony開發與實踐:基于紅莓RK2206開發板